MontyCloud DAY2 Automated Resource Tagging for AWS MAP
Have you signed an agreement to begin migrating to AWS? Or are you a Managed Service Provider (MSP) with an AWS Migration Competency delivering AWS...
MontyCloud DAY2 now offers Single Sign-On (SSO) access for Enterprises that rely on Identity providers (IDP). With this feature, customers can enable secure, reliable, and compliant centralized management of users and user access to the DAY2 platform. In this blog, Sri Santhanam shares how you can easily establish the integration between Azure Active Directory and MontyCloud DAY2 to configure single sign-on access in 5 simple steps.
– Sabrinath S. Rao
Customers can now connect their Azure Active Directory (AD) to MontyCloud DAY2. Users can now sign in using their Azure AD credentials to deploy, operate and manage their cloud applications. This makes it easier for administrators to provide a frictionless enterprise sign-in experience with single-click access to the DAY2 platform.
MontyCloud DAY2 now supports the following SSO configurations.
DAY2 supports all stages of the Single Sign-On (SSO) Configuration lifecycle including options to Create, Update, Delete and Enable/Disable configurations.
For a step by step walk through please check out – How to integrate with Azure Active Directory(AD) as identity provider
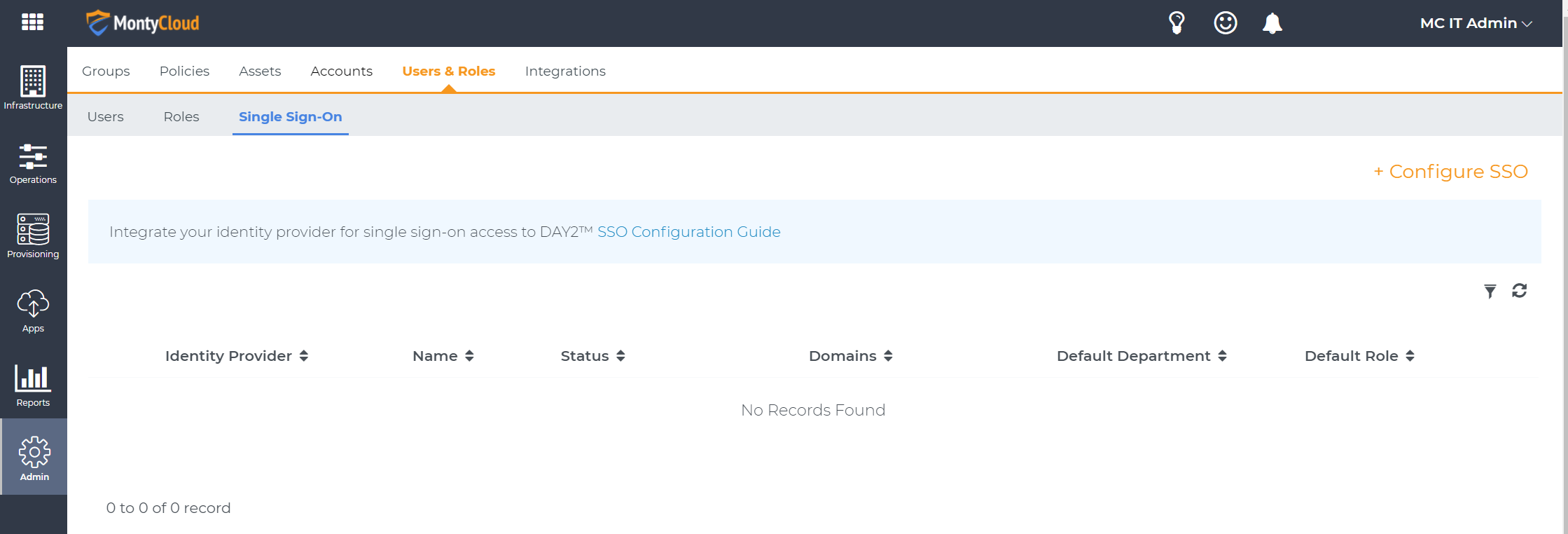
You can configure Single Sign-On (SSO) under the Users & Roles section in the admin area of DAY2 application portal. Click on the Configure SSO action to get started.
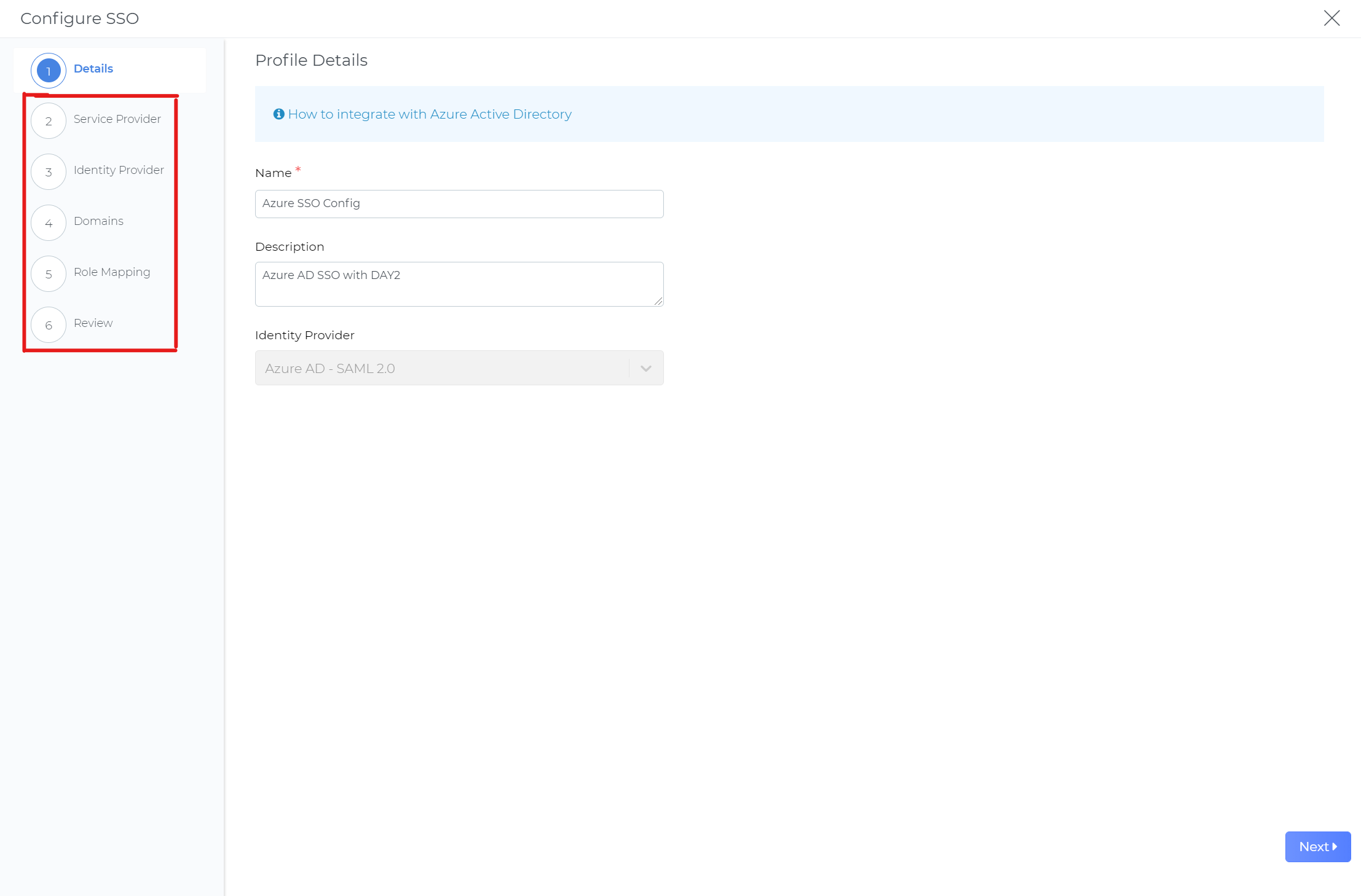
In the Configure SSO wizard, enter a friendly name and description for your SSO configuration. Next, download the Metadata file. You will need to upload this file to your Azure AD DAY2 application setup. Alternatively, you can also upload your Azure AD metadata to DAY2.
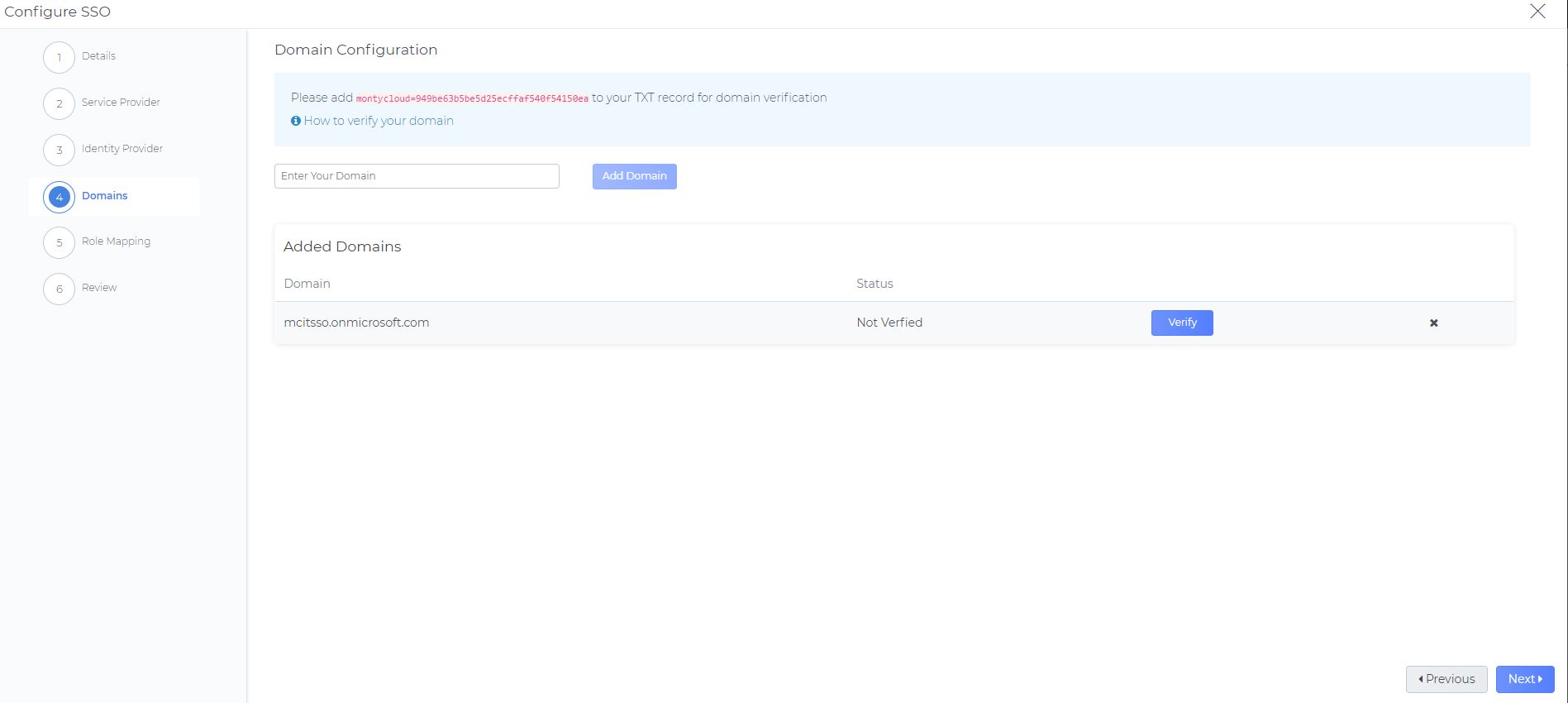
Domain ownership must be verified using DNS “TXT” records. This ensures that we uphold both your security and that of the DAY2 platform. For each domain that you wish to enable SSO, a single TXT record must be created within your DNS zone file and propagated, to allow the DAY2 platform to complete the ownership verification process.
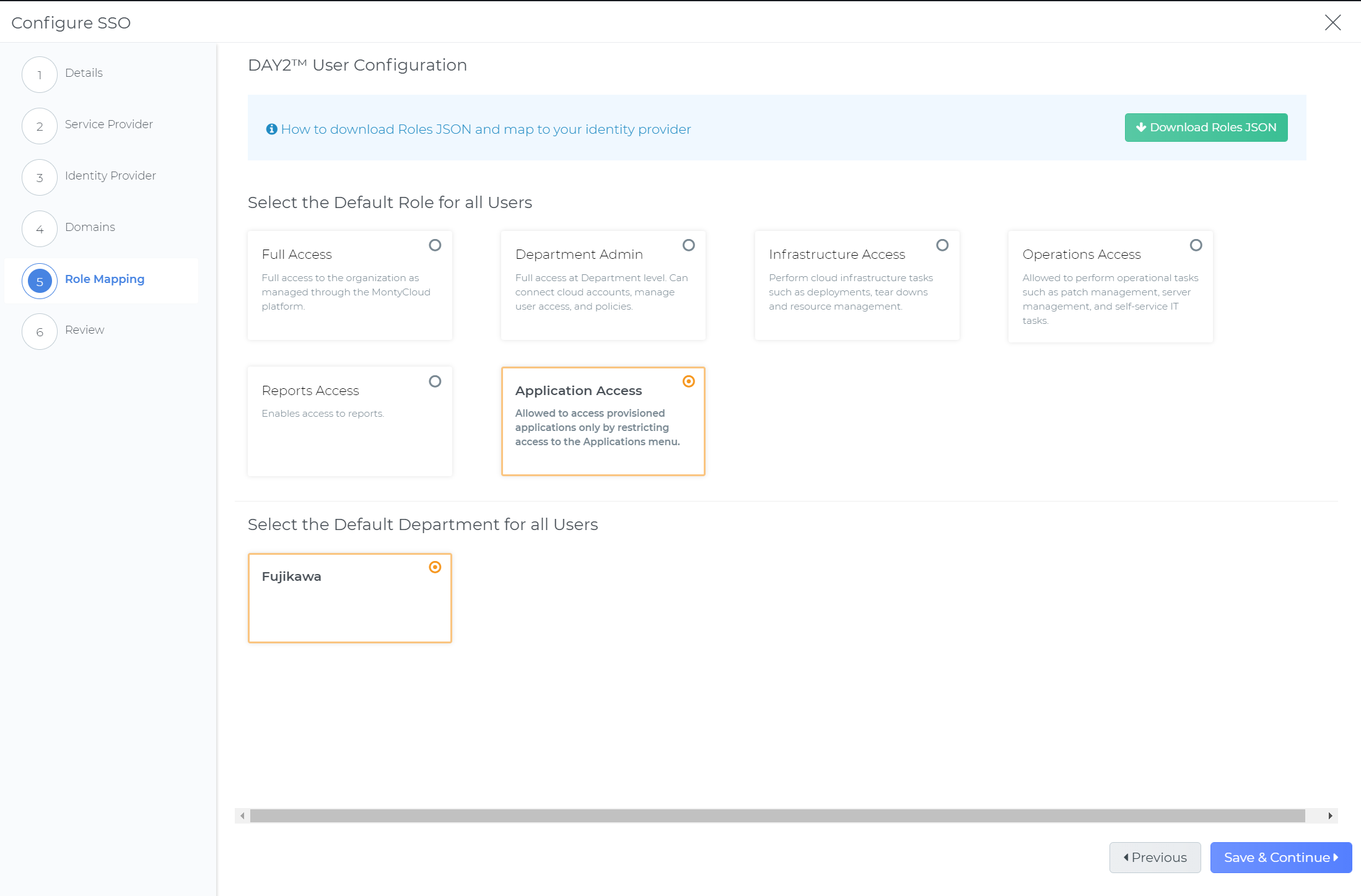
DAY2 authorization is based on Role Based Access Control (RBAC). By integrating the application roles with the Azure AD application manifest, you can ensure users logged in via SSO are mapped to the right RBAC roles in DAY2.
DAY2 also provides default scope while configuring SSO by adding a user defined Department context to all users in the organization. After this is complete, federated users can start sign-on to DAY2 platform to deploy, manage and operate cloud resources and applications. Administrators can change user’s privileges in the user management dashboard.
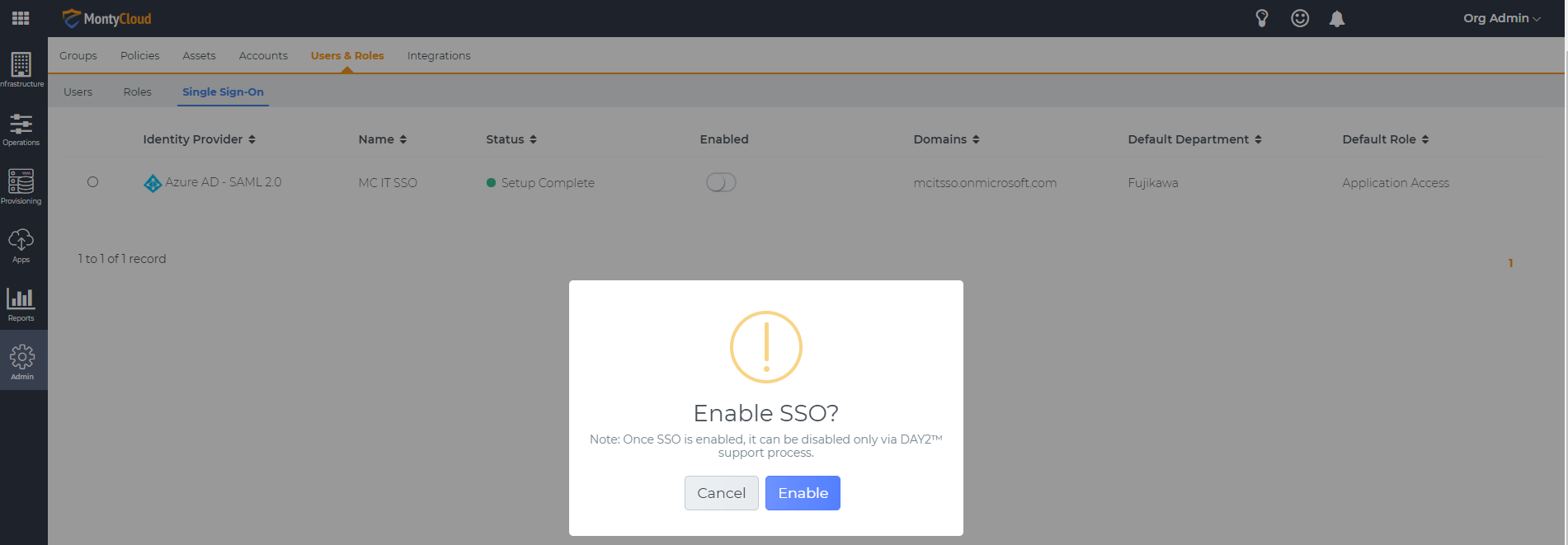
Review and validate your SSO configuration and click Enable. After a confirmation message is displayed your organizations IDP users can seamlessly access the DAY2 platform.
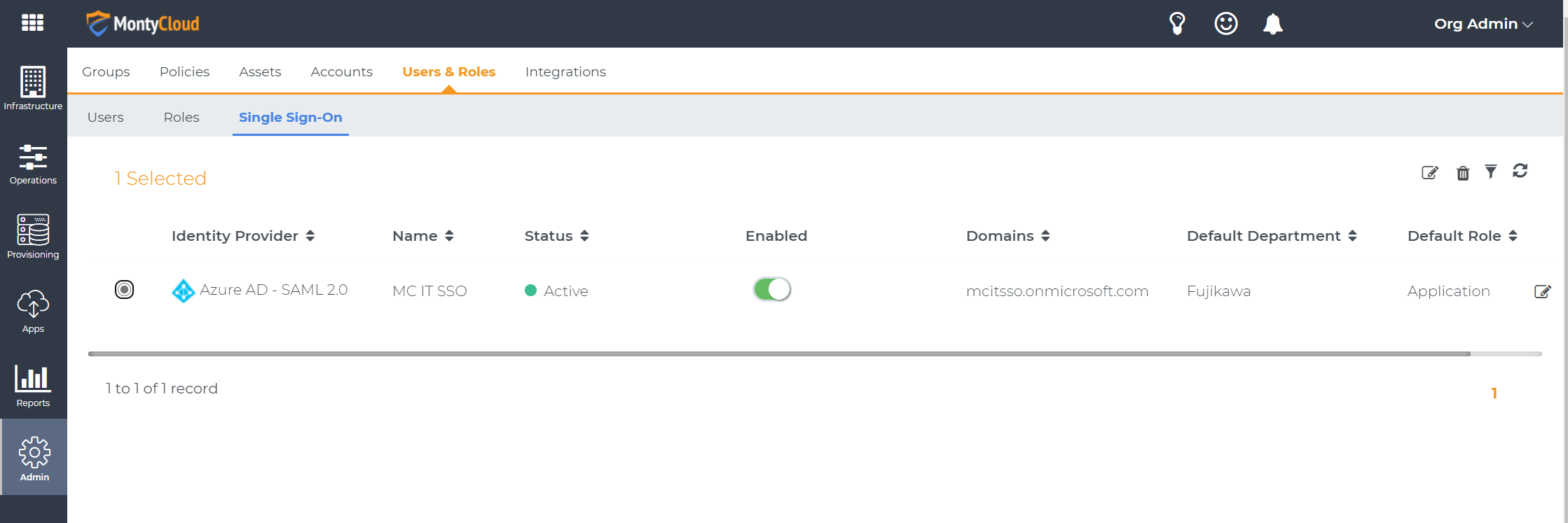
You can also edit your SSO configuration for updating your configuration details such as name, description, IDP information including Certificate and SSO domains by using the edit action and through the same configure SSO wizard.
With this DAY2 platform’s SSO integration with Azure Active Directory, now you can:
Speak to us for any SAML 2.0 Identity provider integration with DAY2 Platform through support@montycloud.com
To learn more about MontyCloud’s DAY2 intelligent Cloud Management Platform, please go to https://www.montycloud.com.


Have you signed an agreement to begin migrating to AWS? Or are you a Managed Service Provider (MSP) with an AWS Migration Competency delivering AWS...
The Imperative of Infrastructure as Code (IaC) Just as blueprints are vital for constructing resilient physical infrastructure, Infrastructure as...

Today I am super excited to announce the availability of MontyCloud’s CoPilot for Cloud Operations, an interactive Agent for simplifying Cloud...